Managed Assets: More Than Just Endpoints
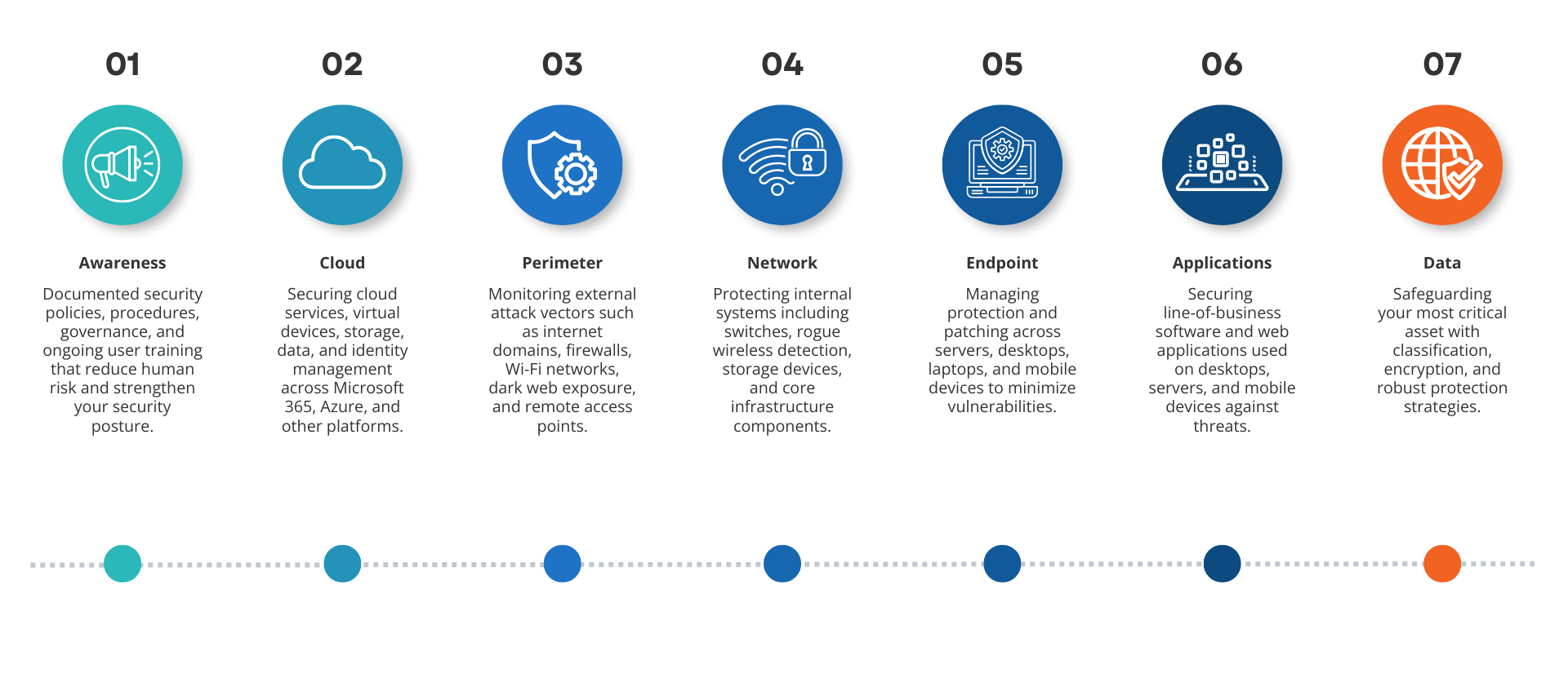
Our comprehensive approach ensures all parts of your attack surface are continuously monitored and secured, reducing risk and strengthening your overall defense.
Our Proven Process
-
FIND
We identify vulnerabilities before attackers do—through deep assessments, threat detection, and continuous monitoring across your environment.
-
FIX
We quickly remediate risks with expert-driven solutions, patching gaps, hardening systems, and aligning your defenses with industry best practices.
-
FORTIFY
We strengthen your security posture long-term by implementing layered protections, automation, and awareness training—building resilience from the inside out.
Why Work With Us
Cybersecurity built on proof, not promises.
Most cybersecurity providers hand you a dashboard and call it protection. We don't. We get into your environment, learn where your real exposure lives, and build defenses that actually hold — across every device, every user, and every workload. Our clients don't just feel safer. They have the evidence to prove it.
Decision Digital transformed our security posture. Their team identified vulnerabilities we didn't even know existed and implemented solutions that keep us protected around the clock.
Sarah M
IT Manager
We were worried about compliance and data breaches. Decision Digital's proactive approach and 24/7 monitoring have kept us safe and confident. They're more than a vendor — they're a trusted partner.
James R
Chief Executive OFficer
We sleep better knowing Decision Digital is monitoring our systems. Their proactive approach stopped two potential breaches before they became disasters.
Emily T
Operations Manager
Related Resources
Cybersecurity Challenges Resolved for Financial Institution
A leading financial institution partnered with us to address rising cyber threats, compliance demands, and internal skill gaps. Through us, they improved protection, reduced incidents, and strengthened regulatory confidence.
How to Build a Strong Security Culture for Leaders
In today’s threat-filled landscape, cybersecurity isn’t just an IT issue — it’s a leadership imperative. Learn how forward-thinking leaders build a culture of vigilance, transparency, and resilience to stay ahead of evolving cyber risks.
Cyber Safety Measures in the Remote Work Era
As remote work becomes the norm, cybersecurity risks are rising. We outline essential strategies to help businesses protect their data, employees, and operations in a distributed work environment.
Let's build a foundation that actually works.
Tell us what operational friction you are trying to solve, and our engineers will help you map out a clear path forward.
For Businesses
If your team is fighting recurring downtime, configuration drift, or patchwork security, we engineer clean, enterprise-grade infrastructure to stabilize your operations.
For MSPs & MSSPs
If you are battling ConnectWise bottlenecks, messy data migrations, or manual workflow backlogs, we provide platform-level expertise to optimize your delivery.


